2015-11-17
OpenSSL comes in handy when you need to generate passwords or random strings. For example for system accounts and services. In this short post I'll give you a quick example on how to generate random passwords with OpenSSL in Linux (Bash), Windows and PHP.

2015-10-08
Here is how you can verify whether an external command in PowerShell was executed successfully or not by checking its errorlevel. Simply by verifying the PowerShell exit code using the $? operator or $LASTEXITCODE.

2015-09-20
Learn how to get the Hyper-V guest virtual machine serial number with PowerShell, this is ideal for automated deployments with WDS or docs

2015-08-08
The Baidu spider (BaiduSpider user agent) can be a real pain to block, especially since it does not respect a robots.txt as it should. This post shows you how to block Baidu Spider bot, using IIS URL Rewrite Module based on its User-Agent string.

2015-07-01
Optimize PHP's OPcache configuration and make OPcache perform even better. After configuring and optimizing PHP's realpath_cache_size, the OPcache cache mechanism is the next step to fine-tune. With just a few tweaks you tune OPcache to perform much better

2015-06-22
Do you host your WordPress website on Windows Server IIS? And are you having trouble with your web.config? Here is mine :)
2015-06-06
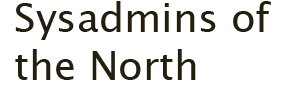
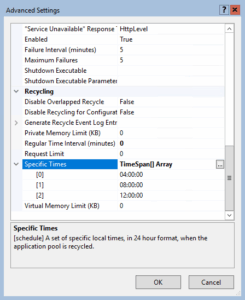
Set up HTTP Strict-Transport-Security (HSTS) response header in Windows Server IIS 10, here is some more technical information about HSTS in IIS, and other security headers...

2015-05-15
Send mail over authenticated SMTP using TLS, in PHP, ASP and ASP.NET. Send email securely from your website. Ready to use examples!

2015-04-28
Have you ever been in a situation where you needed to perform remote administration on a Windows Server, and the RDP port 3389 is blocked on a firewall? You can tunnel RDP over SSH with PuTTY

2015-04-10
Schedule a PowerShell script to monitor local services in your Windows Server environment

2015-04-07
To get and set File Server Resource Manager NTFS quota you now have to use PowerShell FileServerResourceManager cmdlets. It's pretty easy to get directory information with Get-FsrmQuota and change dirquota.exe using Set-FsrmQuota.
2015-04-03
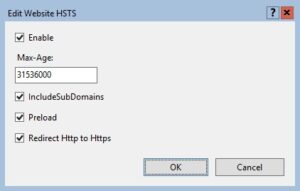
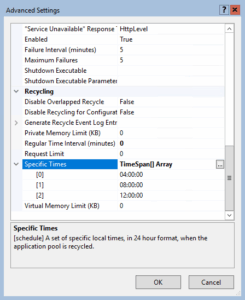
By default, an IIS application pool (or "AppPool") recycles on a regular time interval of 1740 minutes, or 29 hours. One reason for this time interval is that application pools don't recycle at the same moment every day (every day at 07.00 for example).

2015-03-31
A change in PHP's default_charset php.ini setting causes HTML output to break if you try to set a different charset in your HTML head. It also might break functions like htmlentities() and htmlspecialchars().

2015-03-25
Learn how to turn off swap in Bash, because when a swap partition is enabled Linux starts swapping, which may degrade (MySQL) system performance

2015-03-04
Here is how to install software packages during a Windows Deployment Services (WDS) deployment, without Microsoft Deployment Workbench (available in the Microsoft Deployment Toolkit, or MDT).

2015-02-15
In this post you’ll learn about setting up a Monit monitoring service for your websites and services. Monit is a free and open source service monitoring application which can perform various event-based actions. Monit can send email notifications, restart a service or application, or take other responsive actions. We set Monit up on a Ubuntu 14.04 VM, built on Hyper-V. And we use Monit to monitor several websites, and send out notifications on downtime.

2015-01-04
Relive the golden age of PC gaming. Learn how to configure DOSBox on Windows 11 to run classic MS-DOS titles, optimize CPU cycles for period-accurate speed, and set up a custom autoexec.bat menu for easy launching.

2015-01-04
Sometimes you need to find all files owned by a specific user, recursively on your Windows Server NTFS file system. PowerShell has some neat cmdlets to automate this task for you and here is how.

2015-01-02
With thousands spam reactions, disabling (and removing) WordPress comments is often the only way to go. Here is how to disable WordPress comments in both the WordPress Dashboard interface and in your MySQL / MariaDB database.

2014-12-22
Over time, as your Windows Server runs longer, more and more disk space is eaten. Simply gone! Investigating the disk usage leaves you clueless; there are no large log files, crash dumps, or there is no software to be removed. Where did that space go?