Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
The Baidu spider (BaiduSpider user agent) can be a real pain to block, especially since it does not respect a robots.txt as it should. This post shows you how to block Baidu Spider bot, using IIS URL Rewrite Module based on its User-Agent string.
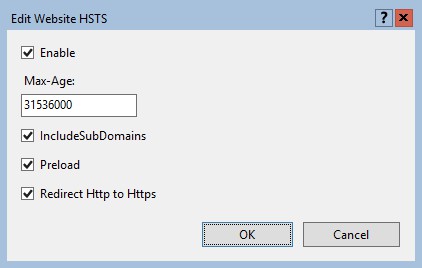
Set up HTTP Strict-Transport-Security (HSTS) response header in Windows Server IIS 10, here is some more technical information about HSTS in IIS, and other security headers...

Windows Server IIS loves to tell the world that a website runs on IIS. It does so with the "Server:" header in the HTTP response, as shown below. In this post I'll show you how to remove HTTP response headers in Windows Server IIS. You don't want to give hackers too much information about your servers, right?.
![[HttpException (0x80004005): The length of the URL for this request exceeds the configured maxUrlLength value.]](https://www.saotn.org/wp-content/uploads/2025/06/Length_of_URL_for_request_exceeds_maxUrlLength_value-11-768x422.png)
The length of the URL for this request exceeds the configured maxUrlLength value is an IIS error telling you the length of the given URL exceeds a limit. The Windows Server IIS maximum URL length is defined by the HttpRuntimeSection.MaxUrlLength property. Its value is 260 characters. This may cause problems with longer URLs, and here is how to resolve this maxUrlLength issue.