Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
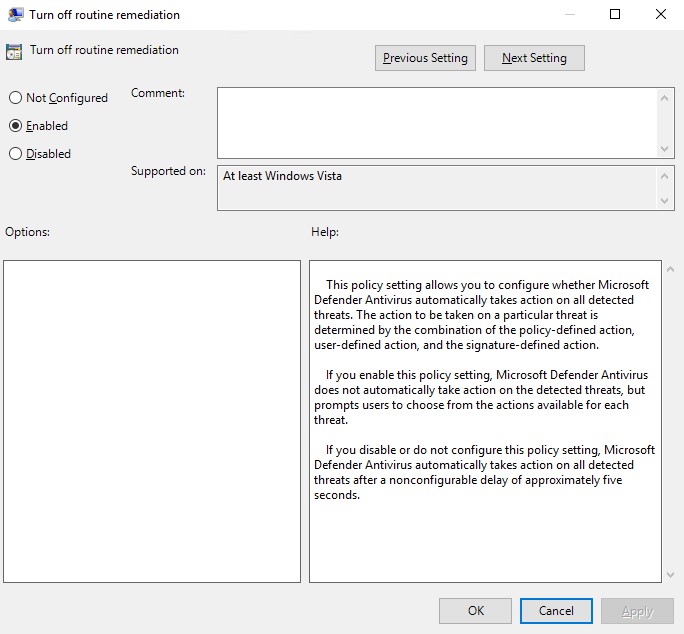
Turn off Windows Defender routine remediation using a GPO setting called “DisableRoutinelyTakingAction”. This policy setting allows you to configure whether Microsoft Defender Antivirus automatically takes action on all detected threats.
Enabling Windows Defender per GPO failed with the error message "Get-MpComputerStatus : The extrinsic Method could not be executed.", here is how to resolve this issue.
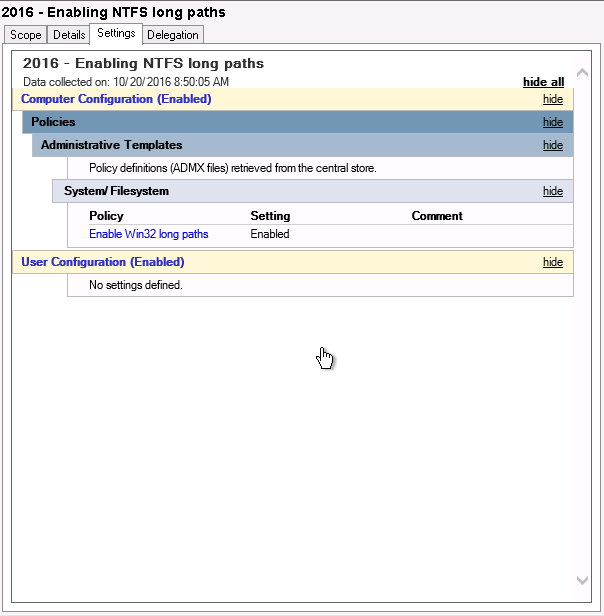
Windows Server 2016 was finally released last week, meaning we can finally lift the idiotic 260 characters limitation for NTFS paths. For this, you use a GPO or Group Policy Object in Windows Server.