IIS backup and restore
Learn how to back up and restore IIS 10 webserver configuration with appcmd.exe and PowerShell
Learn how to back up and restore IIS 10 webserver configuration with appcmd.exe and PowerShell
MySQL Connector/NET and utf8mb4 character set can cause an exception System.Collections.Generic.KeyNotFoundException "The given key was not present in the dictionary".
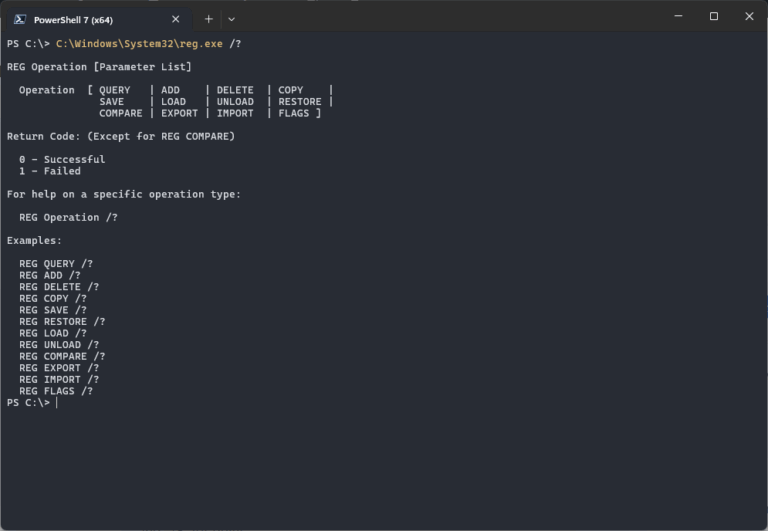
Learn how to silently import a .reg file into your Windows Registry. This neat regedit trick comes in handy quite often. The regedit command is valid for Windows 11, 10, Windows Server 2022, 2019 and older.

3 unique methods to list Service Principal Names (SPNs) in your Windows network quickly using PowerShell. An SPN or Service Principal Name is a unique identity for a service, mapped with a specific account (mostly service account).
If a Windows Server 2016 guest VM on Hyper-V hangs while stopping after Windows Updates, and it won't reboot, it might be caused by the recovery debug information type set. Especially when you have moved the Windows PageFile to a different partition / VHDX
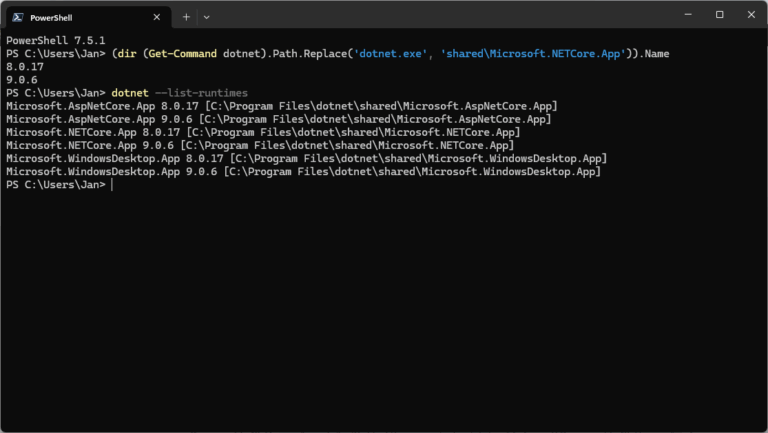
Users can install and run multiple .NET Framework versions on their computers. When you develop or deploy your app, you might need to know which .NET versions are installed on a machine and here is how to check the .NET version.
The postsuper command controls different types of queues in the Postfix mail system, like the deferred or hold queue. This post shows you some Postfix queue operations to maintain your mail servers.

Unzip a file on your PowerShell command-prompt may come in handy sometimes, even on your Windows 11/10 workstation. Use Expand-Archive for this, and all that is required is PowerShell 5.0+, or the .NET 4.5+ Framework to use System.IO.Compression.ZipFile.
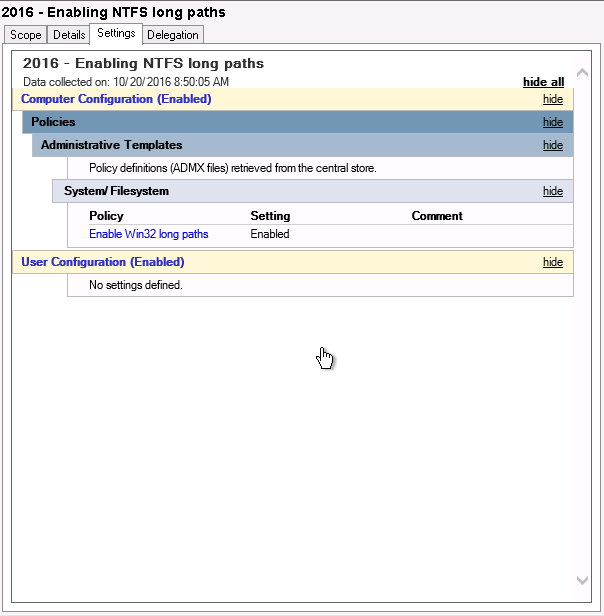
Windows Server 2016 was finally released last week, meaning we can finally lift the idiotic 260 characters limitation for NTFS paths. For this, you use a GPO or Group Policy Object in Windows Server.

In this post I provide you with 5 ways to cleanup files and free up disk space in Windows Server 2016 (and older / newer Windows Server version), without using the Disk Cleanup Utility. Reclaim lots of lost gigabytes easy. Disk space usage is still an issue in Windows Server.