Security
Disable ECDH public server param reuse in Windows Server IIS
Windows Server IIS is known for reusing DH key values, but there is a way to disable ECDH public server param reuse in Windows Server IIS and here is how.

Create strong passwords in Windows
Learn how to create strong and unique passwords in Windows using PowerShell, because the use of those unique and strong passwords is important.

Calculate SHA-256 checksums in PowerShell
Learn how to calculate and create file checksums with PowerShell's Get-FileHash and certutil.exe. Use this to validate file integrity in Windows (Windows Server).

Install SSL / TLS certificates in Windows Server using PowerShell
The following PowerShell snippet can be used to quickly install an SSL (or TLS) certificate in Windows Server. It assumes you have a PFX file and its password. The default location is Cert:\LocalMachine\My, to use for IIS websites.

Blocking bad bots and search engines using .htaccess
Take control of your server resources by learning how to block aggressive bots and unwanted search engines using .htaccess and mod_rewrite. This guide provides copy-paste ready configurations to prevent bandwidth theft, stop scrapers, and ensure that only relevant search engines crawl your website.

YubiKey support in OpenSSH for Windows 11
Secure your Windows 11 environment by moving SSH private keys to hardware. Learn how to configure YubiKey FIDO2/U2F support in native OpenSSH, manage the ssh-agent, and eliminate file-based credential risks.

Quickly check EnableTrailerSupport isn’t set in your network for http.sys (CVE-2022-21907)
Find out fast if your IIS webservers have EnableTrailerSupport enabled for https.sys in the registry. Here is a small PowerShell method.

3 Ways of blocking sendmail.php on IIS webserver
Here are 3 ways of blocking access to a PHP sendmail.php script on your Windows Server IIS webserver. This comes in handy if a websites on your webserver sends out spam and you need to block access to a script on a specific website or globally in IIS.

Retrieve SSH public key from Active Directory for SSH authentication
Storing SSH public keys in Windows Server Active Directory gives you a single location where you manage public SSH keys instead of on numerous separate servers. This is easier than distributing and managing numerous unmanaged authorized_keys files across your network and servers.

Add, list and remove IP addresses in Windows Firewall
How to bulk add IP addresses in Windows Firewall, list an IP address and how to remove all IP addresses from Windows Defender Firewall with Advanced Security

Block brute force attacks on SQL Server, block IP addresses in Windows Firewall using PowerShell
For the time being, some manual labor is involved, but it is still manageable. You can use this to create your own solution to block offending IP addresses in SQL Server’s firewall.
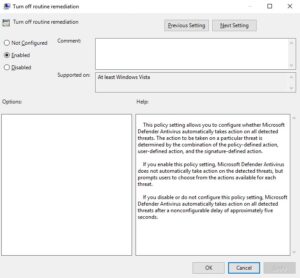
Windows Defender: Turn off routine remediation (DisableRoutinelyTakingAction)
Turn off Windows Defender routine remediation using a GPO setting called "DisableRoutinelyTakingAction". This policy setting allows you to configure whether Microsoft Defender Antivirus automatically takes action on all detected threats.

How-to fix Windows Defender error “Get-MpComputerStatus : The extrinsic Method could not be executed.”
Enabling Windows Defender per GPO failed with the error message "Get-MpComputerStatus : The extrinsic Method could not be executed.", here is how to resolve this issue.
Force HSTS in Apache .htaccess
Learn how to enable HSTS (HTTP Strict Transport Security) in Linux Apache .htaccess. I wrote about enabling HTTP Strict Transport Security (HSTS) in IIS earlier. But what about enabling HSTS in Apache .htaccess? Here is how.

Easily find out which Windows Updates are installed with PowerShell
Easily find out whether an update or patch is installed. Or not... With PowerShell

Find vulnerable WordPress plugin versions fast using PowerShell
Find vulnerable WordPress plugins fast using PowerShell on Windows Server and IIS

Disallow direct access to PHP files in wp-content/uploads/
Securing the WordPress uploads folder is important. In many hacked WordPress sites, a PHP backdoor is found within the WP_CONTENT_DIR/uploads directory. Often because this is the location where uploads are placed automatically. From the backdoor within wp-content/uploads other backdoors are uploaded to various locations, and scripts are injected with malware.

.htaccess security best practices in Apache 2.4.6+
Since Apache 2.4.6, a new module is used to configure and set up access control for websites: mod_authz_core. This means you have to use a different syntax for allowing or blocking hosts and IP addresses to your website. Apache Access Controle done right in WordPress .htaccess.

Protect WordPress from brute-force XML-RPC attacks
How to protect your WordPress from brute-force XML-RPC attacks, because the WordPress XML-RPC API has been under attack for many years now.