Posted inWeb applications
Disable Joomla Contacts component (com_contact) in MySQL / phpMyAdmin
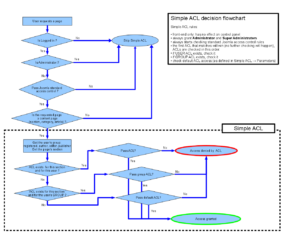
How-to disable Joomla's built-in contact forms component and its ability to send a copy to the sender, directly in your MySQL database using phpMyAdmin.