2021-09-20
For the time being, some manual labor is involved, but it is still manageable. You can use this to create your own solution to block offending IP addresses in SQL Server’s firewall.
2021-09-14
Native support for HTTP/3 in Windows Server 2022, jeej! Host HTTP/3 web services in Windows
2021-09-14
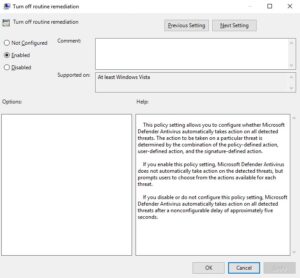
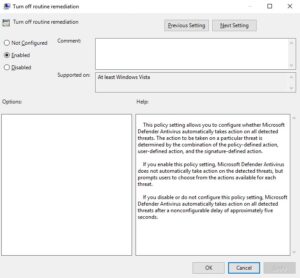
Turn off Windows Defender routine remediation using a GPO setting called "DisableRoutinelyTakingAction". This policy setting allows you to configure whether Microsoft Defender Antivirus automatically takes action on all detected threats.

2021-09-05
Here is how you can share your SSH keys between Windows 11/10 and WSL 2 if you don't want to copy over your ssh keys from Windows to WSL 2 Linux, or generate new ones.
2021-08-30
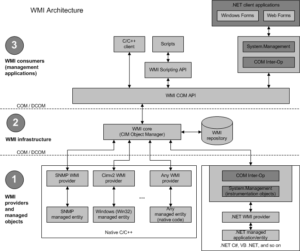
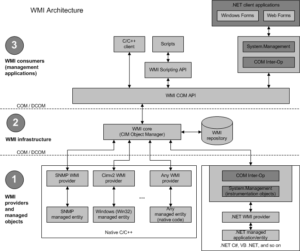
Learn how to fix memory issues and subsequent crashes in WMI / WmiPrvse.exe by increasing available memory and handles

2021-05-05
Enabling Windows Defender per GPO failed with the error message "Get-MpComputerStatus : The extrinsic Method could not be executed.", here is how to resolve this issue.
2021-04-22
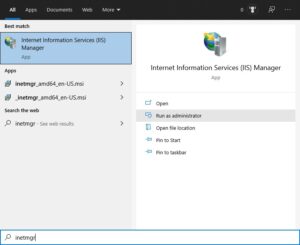
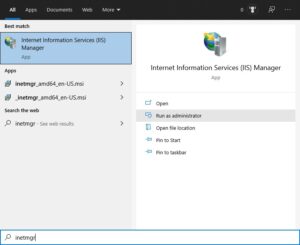
Use IIS Manager to administer various components of your website through a graphical user interface (GUI) if it's hosted in Windows Server IIS. In this article you'll learn how to install and setup IIS Manager in Windows 11/10 to manage your website(s).

2021-04-16
If you want to quickly delete all saved Remote Desktop credentials from your Windows 10 Credentials Manager, here...

2021-04-14
Zabbix monitoring for your websites and ASP.NET applications in IIS using _Process Performance Counter.

2021-02-27
When you host multiple websites in IIS, and you need to monitor them, Zabbix is one of your options. In Zabbix, you can take advantage of Windows Server performance counters. And in this article I show you some important Windows performance counters you can use to monitor your ASP.NET web application in Zabbix.

2021-02-27
Here is a small introduction to query the number of running w3wp.exe processes per IIS application pool in Zabbix so you can start monitoring Microsoft Windows Server IIS with Zabbix.

2020-12-22
PowerShell ternary operator emulation for PowerShell 5.1. Quick and dirty determine if a condition is true or false by emulating the ternary operator. For example when determinering if the server you are servicing is a Windows Server Desktop Experience version or not (and thus Server Core).
2020-12-18
Learn how to enable HSTS (HTTP Strict Transport Security) in Linux Apache .htaccess. I wrote about enabling HTTP Strict Transport Security (HSTS) in IIS earlier. But what about enabling HSTS in Apache .htaccess? Here is how.

2020-12-09
Easily find out whether an update or patch is installed. Or not... With PowerShell
2020-11-09
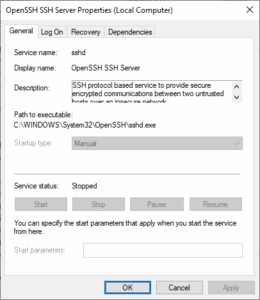
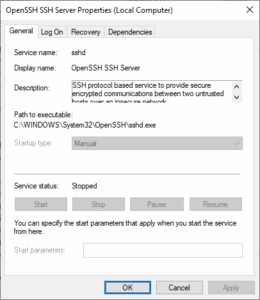
Microsoft have released their OpenSSH port for Windows Server and Windows 10 back in 2015. Here is how to install the OpenSSH Server on Windows Server 2022, 2019 and 2016.

2020-10-22
Follow this if you have no more need for Windows Server IIS and want to remove IIS completely from Windows Server using PowerShell
2020-09-24
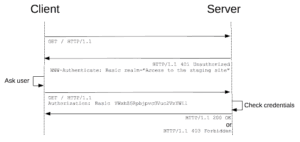
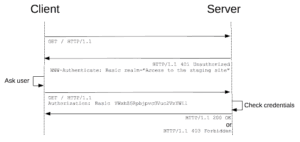
HTTP Basic Authentication managed module for IIS enables HTTP Basic Authentication with virtual user support in Windows Server IIS.

2020-09-18
WSUS uses BITS for downloading updates, and it does so in background mode. Unfortunately, this utilizes remaining bandwidth of the server instead of its full capacity. To speed up WSUS downloads, you can configure BITS in WSUS to use foreground priority.
2020-07-25
Using WSL 2 it is pretty easy to install Hugo in Windows, setting up your local webdevelopment environment and configure Hugo to listen on your Ubuntu's IP address, here is how.

2020-06-02
When you migrate a file server and transfer data, you may need to recreate junction points, as they cannot be copied using (for example) Robocopy.exe. This makes it a must to know where you have junction points, and NTFS hard and soft links. This is where PowerShell comes to the rescue.